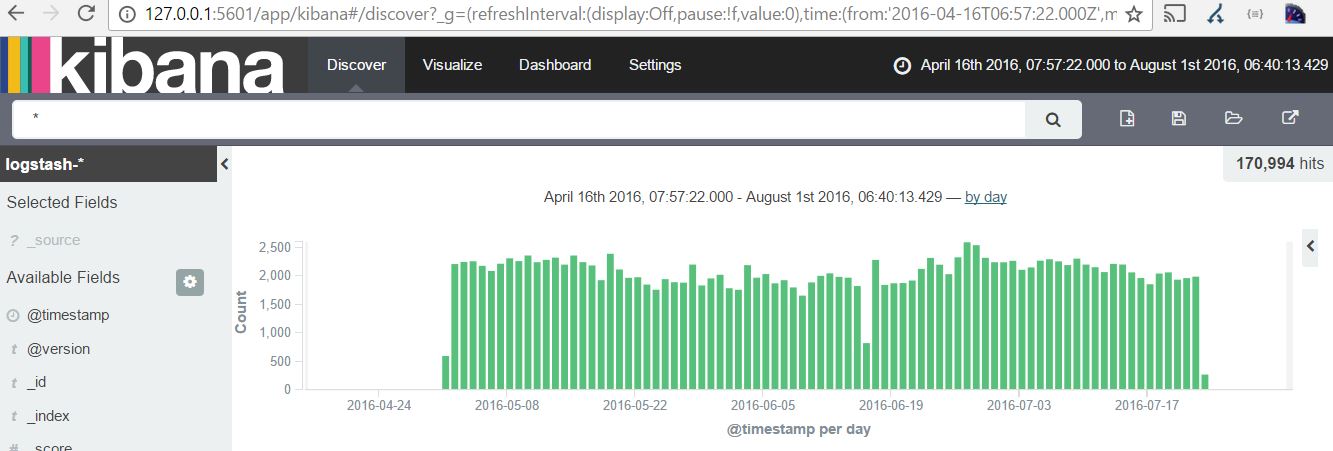
vDOS was a booter service ran out of Israel allowing anyone to DDOS victims. In July 2016 Brian Krebs obtained a database dump from the booter service giving insight into the techniques used and victims of the service.
You can see Brian’s posts here:
https://krebsonsecurity.com/2016/09/alleged-vdos-proprietors-arrested-in-israel/
https://krebsonsecurity.com/2016/09/israeli-online-attack-service-vdos-earned-600000-in-two-years/
To analyse the database I’ve written a Vagrantfile which installs the ELK stack and uses logstash to put the vDOS log file into Elasticsearch, Kibana can then be used to analyse the data.
The Vagrantfile and provision script can be found here:
https://github.com/thomasweaver/vdos-elasticsearch-vagrant
NOTE: The database is not provided here. You must obtain it yourself and copy it the vagrant folder with name attacks.txt The memory is set to 4GB in the Vagrantfile, make sure you have enough memory before doing a vagrant up
git clone https://github.com/thomasweaver/vdos-elasticsearch-vagrant.git
cd vdos-elasticsearch-vagrant
cp location-of-attack-database attacks.txt
vagrant up
Kibana can then be access on
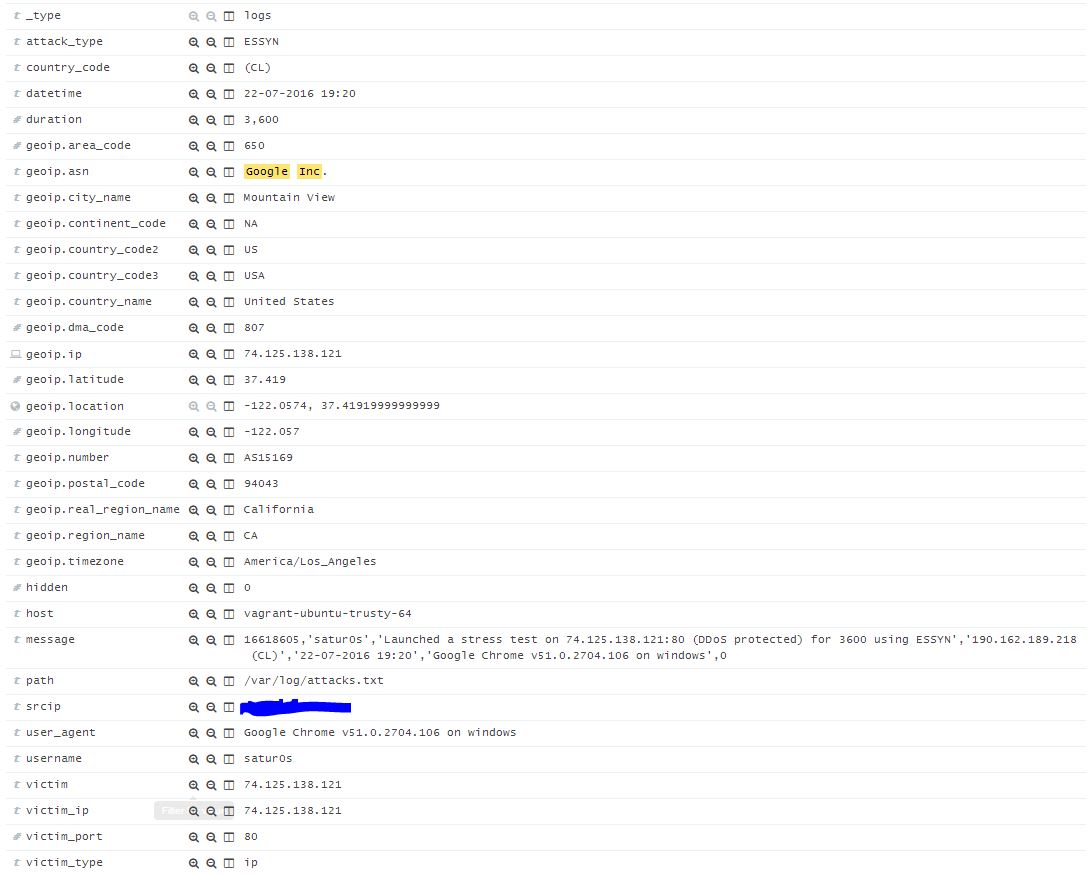
You can then search for your IP, ASN, Company Name or URL.
The above shows a search for “Google Inc” and then an individual log entry